ECDSA Cryptography’s Role in Securing Cryptocurrencies
Exploring the world of the artist known as ECDSA
Cryptocurrencies have revolutionized the financial world, offering a decentralized and secure means of transferring value and executing transactions. Cryptocurrencies leverage cryptographic signatures to ensure that only the rightful owner of a private key can initiate transactions and prevent unauthorized access to funds. The primary cryptographic algorithm used in many blockchain based systems including Bitcoin and Ethereum, Binance Smart Chain, and Avalanche is Elliptic Curve Digital Signature Algorithm (ECDSA). In this post we review ECDSA and how it secures cryptocurrencies.
Beyond cryptocurrencies, ECDSA is also employed in secure communication protocols like Transport Layer Security (TLS) and Secure Shell (SSH). In these settings, ECDSA serves to authenticate the messages exchanged between clients and servers to ensure that the parties involved in the communication are who they claim to be and that the data transmitted has not been tampered with.
Overview of Elliptic Curve Digital Signature Algorithm
The ECDSA used by Bitcoin is based on a particular elliptic curve called secp256k1 and it plays a central role in securing crypto transactions by ensuring the security of crypto funds and verifying the authenticity of transactions.
ECDSA provides the foundations and mechanisms for users to sign their transactions with a private key, which is then verified by other nodes on the network using a corresponding public key. This process guarantees that only the rightful owner of the funds can initiate a transaction, and it also ensures that the transaction details, such as the amount and recipient, remain unaltered during the transfer.
What is an Elliptic Curve?
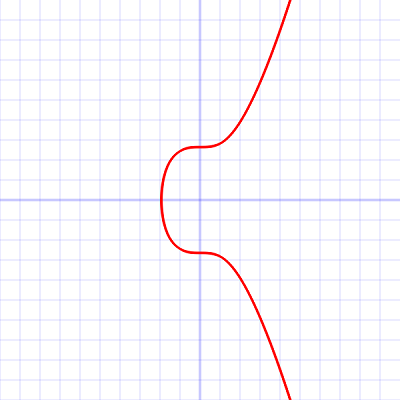
Elliptic curves are special form of a mathematical curve defined by an equation like y^2=x^3+ax+b. As mentioned above, Bitcoin, uses a specific curve called secp256k1 – see image below. In simple terms, an elliptic curve provides a one-way math function that is easy to use forward, but is practically impossible to reverse, ie. It is nearly impossible to crack the algorithm.
secp256k1 has gained popularity because its structure makes computation more efficient, often more than 30% faster than other curves, if the implementation is sufficiently optimized.
ECDSA in Action
ECDSA is used to create digital signatures that digitally “sign” crypto transactions, so that anyone can check that the transactions truly came from the owner of the coins, without learning the private key. In this way transactions are protected so they cannot be altered during transmission. The signing process looks like this – think of this as the “generic” process. Below we will outline more specifically how blockchain wallets execute transactions using a similar process.
Generate a key pair - secret private key (only you know this key), and a public key that others can see.
Build a crypto transaction and hash it.
Produce a signature (r,s) for that hash – your wallet and ECDSA does this
Broadcast the transaction plus signature to the network.
Verify signature - recipient (and anyone else for that matter) uses your public key and the same hash to verify that the signature on the transaction is valid, proving you authorized the transaction. The transaction can then be executed.
Generate keys (once per wallet)
When you create a new crypto wallet, it does two main things with ECDSA. First it picks a large random secret number- this is your private key (which is never shared). Elliptic-curve math is then applied to compute a matching public key from the private key. Public keys are shared. Anyone can know your public key (or an address derived from it), but only you know the private key, and the underlying ECDSA math makes it practically impossible to go backwards from public key to compute the private key.
Create a transaction
To spend crypto coins, your wallet builds a transaction message that includes things like:
Which coins/UTXOs you are spending.
Who you are sending them to – a recipient address.
How much you are sending, and any change back to yourself.
UTXOs are Unspent Transaction Outputs used by Bitcoin and other blockchains, and they represent distinct amounts of cryptocurrency received in a wallet but not yet spent – aka like cash in your pocket.
The wallet then “hashes” the transaction data through a cryptographic hash function (a mathematical function) that generates a fixed sized string of characters – called a hash value, or simply a “hash”. Bitcoin uses the SHA-256 hash.
Create the signature - Sign the transaction
Using your private key and the transaction hash, the wallet computes an ECDSA signature. In simple terms this computation looks like this:
The wallet picks a fresh random number “k” for this signature only (never reused). This random number is known as a nonce and it is generated for each signature to ensure that each signature is unique and prevents predictable patterns.
Elliptic-curve math is applied with “k” to compute a point on the elliptic curve and that is a number “r”. It combines “k”, the transaction hash, and your private key in a formula to compute another number called “s”. The signature is the pair (r,s), which gets attached to the transaction.
Anyone who sees the transaction sees the transaction data, your public key (or a form of it), and the signature (r,s), but still cannot recover your private key. The hash is what gets “signed” by ECDSA and this ensures that any change in the transaction changes the hash making the change detectable – aka if someone/something messes with your transaction, that can easily be detected, and the transaction can then be invalidated.
Send/broadcast the signed transaction
You are now ready to execute the transaction. Your wallet packages the transaction data plus the ECDSA signature (and usually the public key or a reference to it) and broadcasts this package to the cryptocurrency network (nodes and miners/validators).
Nodes that receive the transaction do not trust it blindly; they treat it as a “claim” that you authorized spending those coins, and they then check/verify the signature in the transaction to prove the transaction is legitimate.
Verify the signature
Each node performs ECDSA verification using the transaction data (to recompute the hash), the public key corresponding to the claimed sender, and the signature (r,s). Essentially the verification is simply confirming (or not) that the signature in the transaction matches the hash and the public key under the ECDSA rules.
If the verification passes, the node is convinced the transaction was made by someone using the correct private key (aka the public and private keys are a legitimate key pair). The node is also convinced that the transaction data was not changed after signing, because any change would alter the hash and that invalidates the signature. The transaction can then be executed onto the blockchain.
If verification fails, nodes reject the transaction as invalid, preventing the transaction from executing onto the blockchain.
Public-Private Key Pairs – The Keys (literally) to the Bitcoin Kingdom
Public-key cryptography is a form of asymmetric cryptography where two mathematically related keys play different roles vs. symmetric cryptography which involves the sharing of one secret key by both a sender and a receiver.
Public-key cryptography is a foundational technology and mechanism used to secure a vast array of systems including securing data transport over the Internet via HTTPS / TLS, securing email (PGP, S/MIME), digital signatures, time‑stamping and audit trails, software updates and code signing >> and of course securing blockchain powered digital cash, tokens, smart contracts, stablecoins, and NFTs etc.
Each key pair consists of a public key and a corresponding private key. The public keys can be disseminated widely and openly, and only the corresponding private keys need to be kept secret.
Key pairs are generated with cryptographic algorithms based on hard to solve mathematical problems termed one-way functions. A public‑private key pair is generated together by an algorithm (RSA, ECC, etc.) so that the keys are linked by a hard mathematical problem (e.g., factoring, elliptic‑curve discrete log). A private key is essentially a randomly generated number. A public key is a number that directly corresponds to a private key. A public key can be calculated from a private key, but not vice versa.
Weaknesses
As with all security-related systems, there are various potential weaknesses in public-key cryptography. Aside from making a poor choice of a key generating algorithm or selecting a key length too short, the greatest risk is that the private key gets exposed.
With the advent of quantum computing, many asymmetric key algorithms are considered vulnerable to attacks, and new quantum-resistant schemes are being developed to overcome the problem. Researchers and crypto experts the world over are working on new cryptography methods and algorithms to address this quantum risk. See this post on Post Quantum Cryptography.
How does Bitcoin leverage ECDSA? A quick overview of a Bitcoin Transaction
In very simple terms - a Bitcoin wallet is essentially a manager of key pairs and addresses. Wallets are designed to implement ECDSA as well as provide some extra bookkeeping and coordination capabilities.
Bitcoin uses ECDSA for ownership and authorization of spending. When someone pays you with Bitcoin, the output script “locks” the incoming coins to a condition involving your public key or address. Essentially it provides a signature that verifies against your public key. When you spend coins, your wallet builds a new transaction and provides an ECDSA signature (and usually the public key) that satisfies locking script conditions.
Wallets generate private keys with a cryptographically secure random generator and derive public keys and addresses from them. Many wallets use HD (hierarchical deterministic) schemes so many keys are derived from a single master seed, making backup easier.
In creating transactions, a wallet decides which UTXOs to spend, constructs a transaction, and hashes the relevant parts to get the message to sign. It signs with the corresponding private key using ECDSA, producing a signature and includes the public key as needed in the scriptSig script.
ScriptSig is the unlocking script in a Bitcoin transaction input. It provides the data (like signatures and public keys) needed to satisfy the locking script (ScriptPubKey) from a previous unspent transaction output (UTXO). ScriptSig works in tandem with the ScriptPubKey script to validate spending.
In simple terms, a Bitcoin wallet’s main job is to keep your private keys safe, construct correct transactions, and run ECDSA correctly for each input to verify and execute transactions.
Wrapping up
ECDSA provides secure and efficient digital signing and verification processes for crypto transactions. It has established itself as the standard for securing transactions in major blockchain networks – for now!
As briefly mentioned, the alarm bells are now ringing about the pending and serious risk posed by quantum computing and its potential for cracking existing crypto algorithms and related technologies, including ECDSA! Bottom line - blockchain networks will need to evolve, refine and adopt new cryptographic techniques to prevent being compromised by future quantum computing systems. The good news is that the crypto industry has recognized this challenge and the work to transition to new cryptography algorithms is underway.
Thanks for reading! Please, share your thoughts via the Comments section for this post or open a new SubStack chat thread … and please forward this post to your friends and colleagues. Until next time!